TRAFFIC ANALYSIS EXERCISE - TECSOLUTIONS
2020-07-31 - TRAFFIC ANALYSIS EXERCISE - TECSOLUTIONS
学习记录
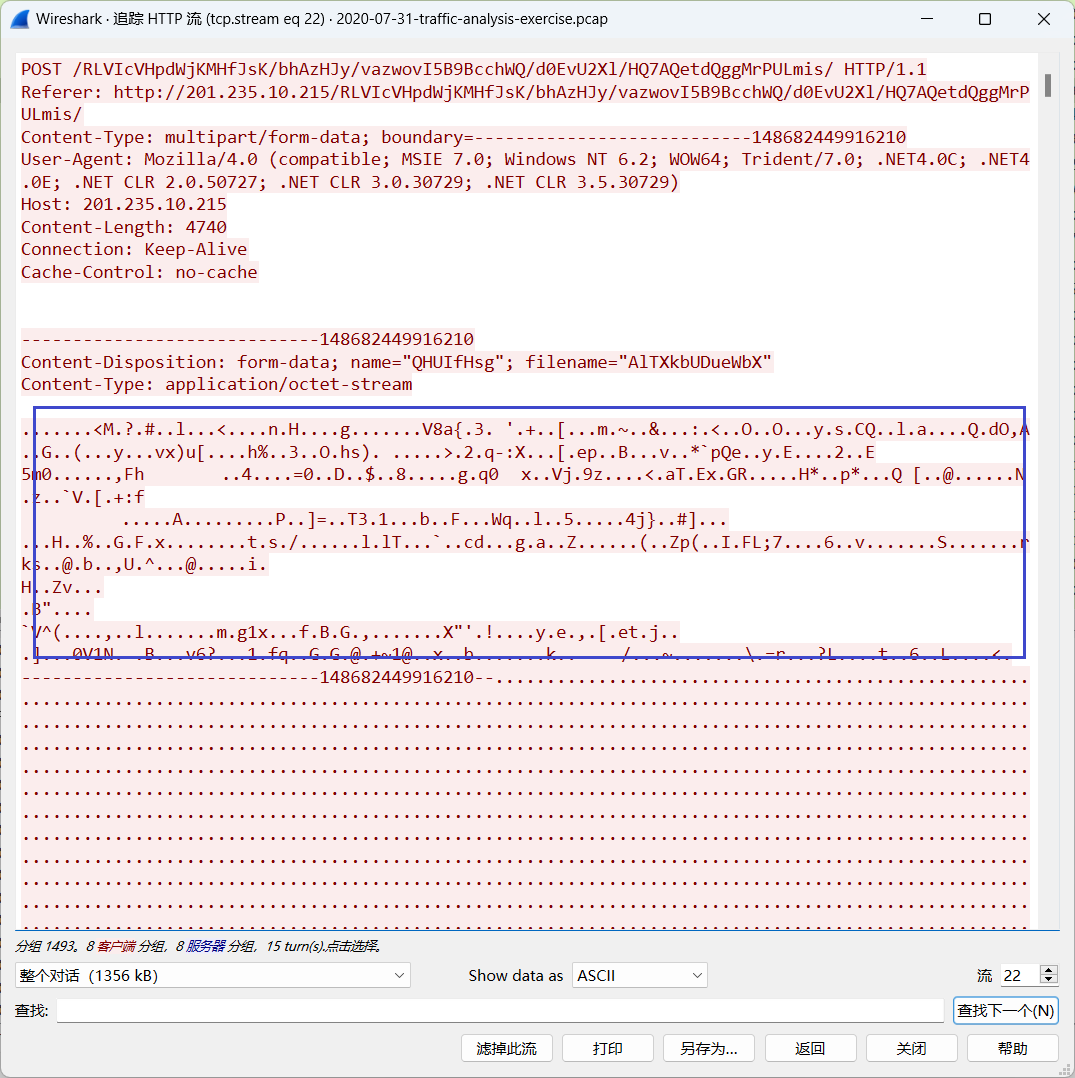
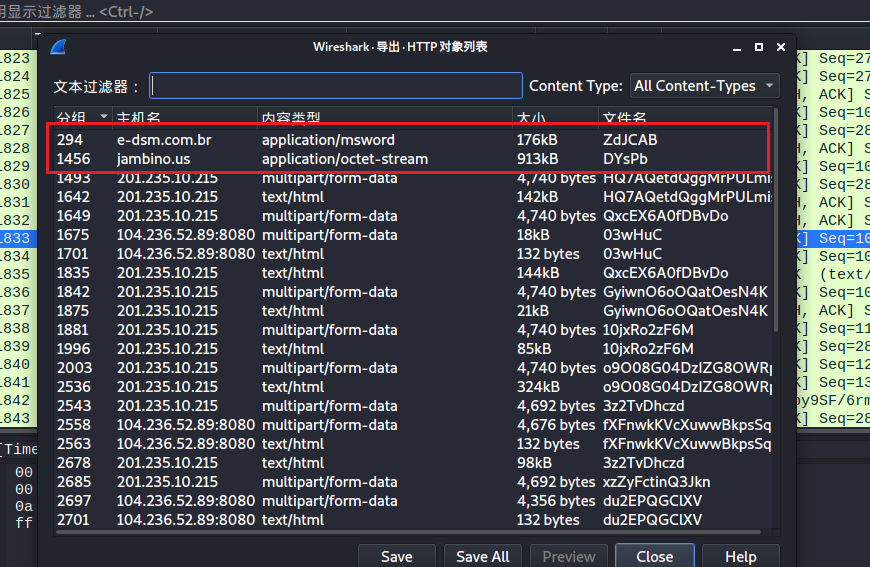
HTTP流
首先过滤HTTP流并追踪
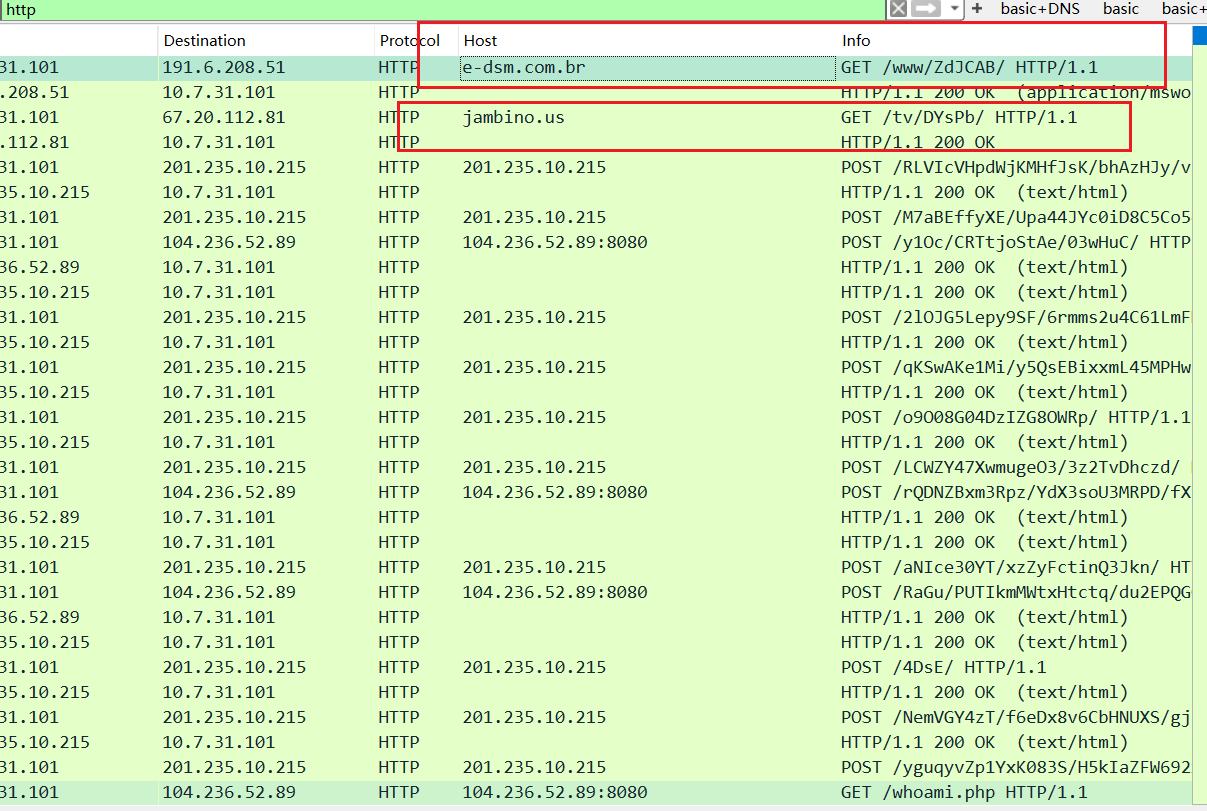
发现域名e-dsm.com.br返回了一个doc文件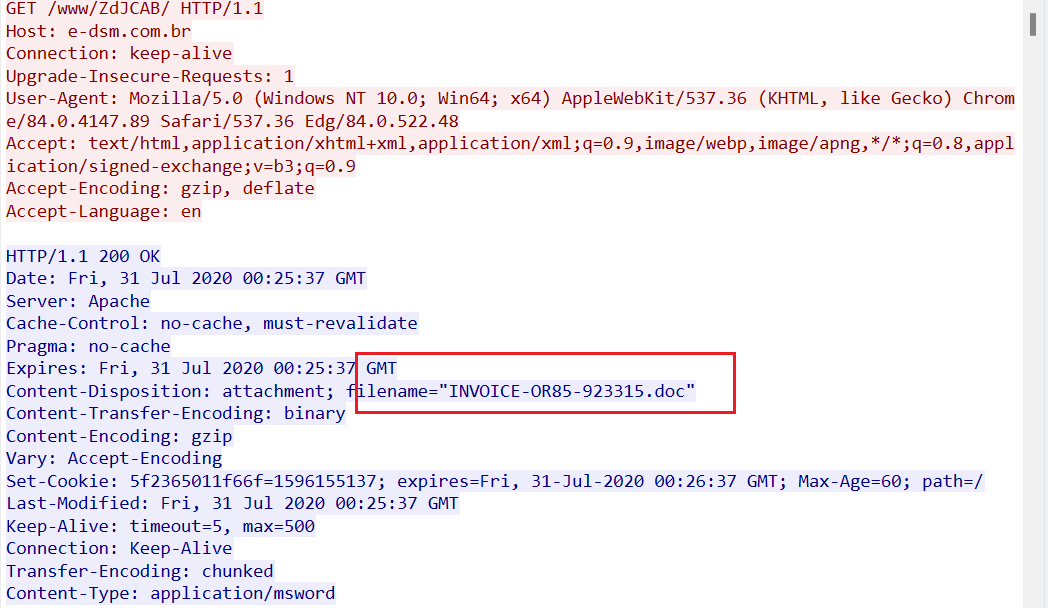
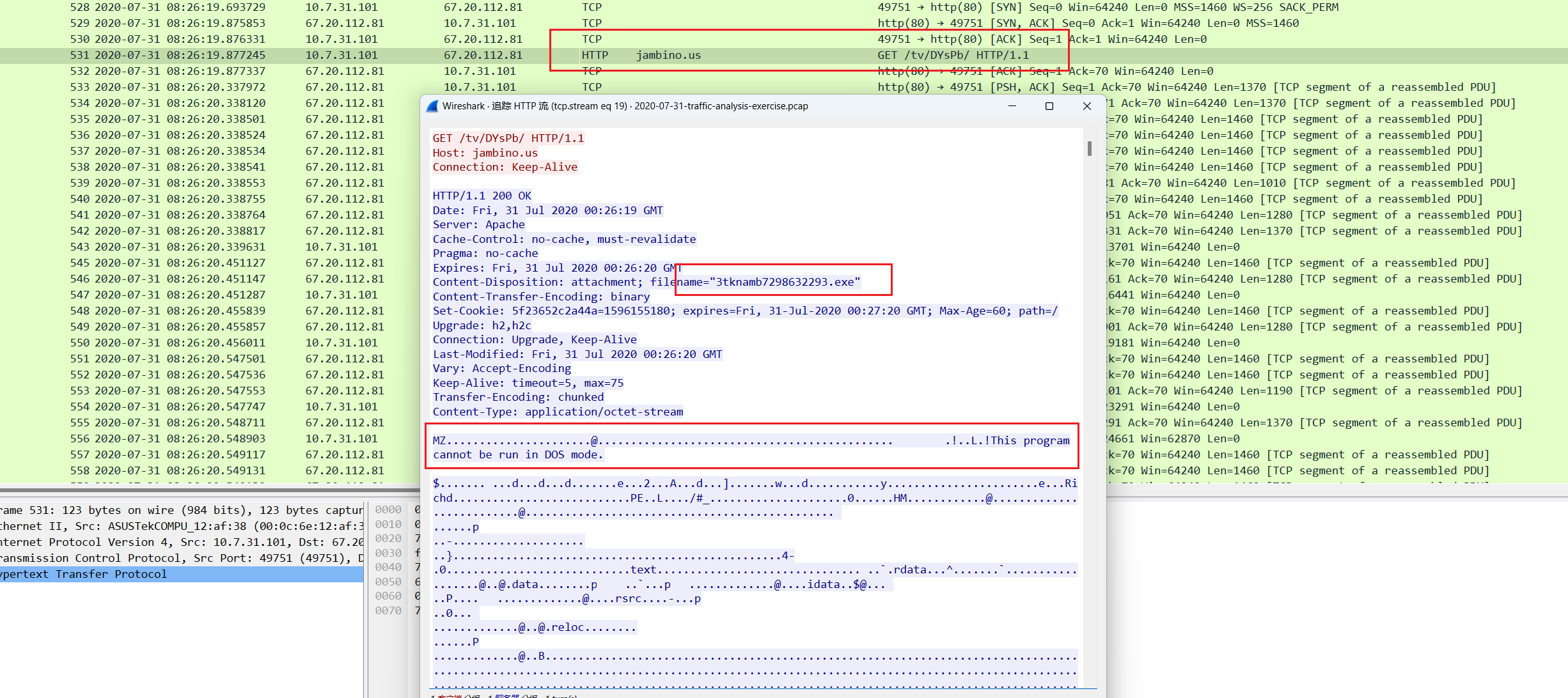
域名jambino.us返回了一个exe可执行文件
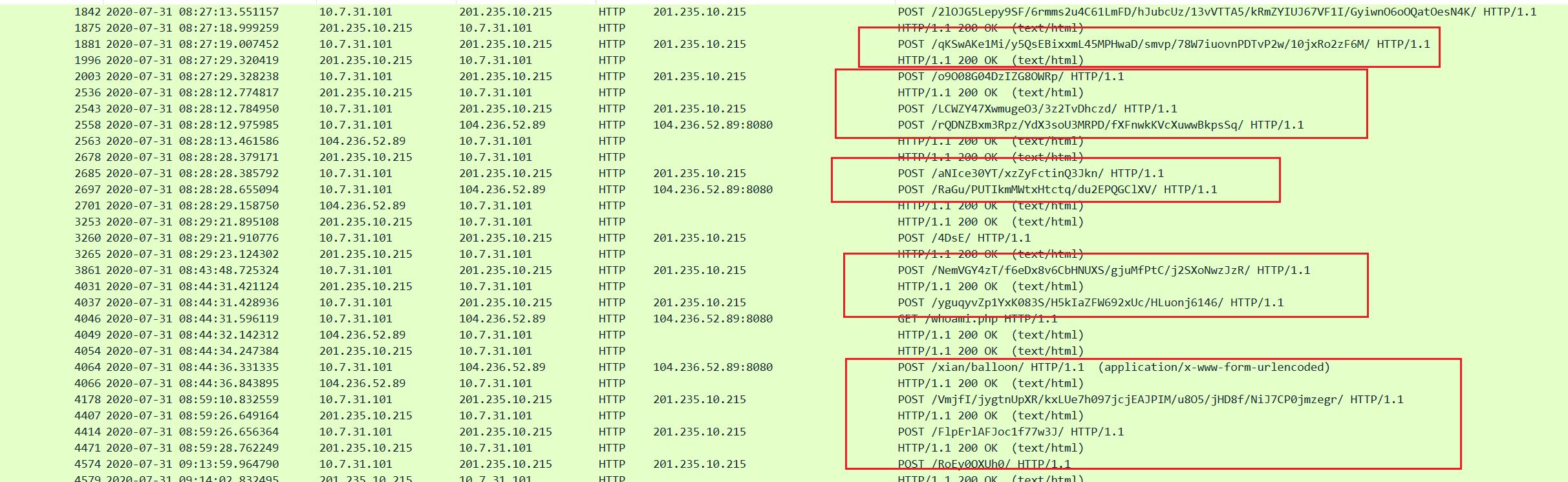
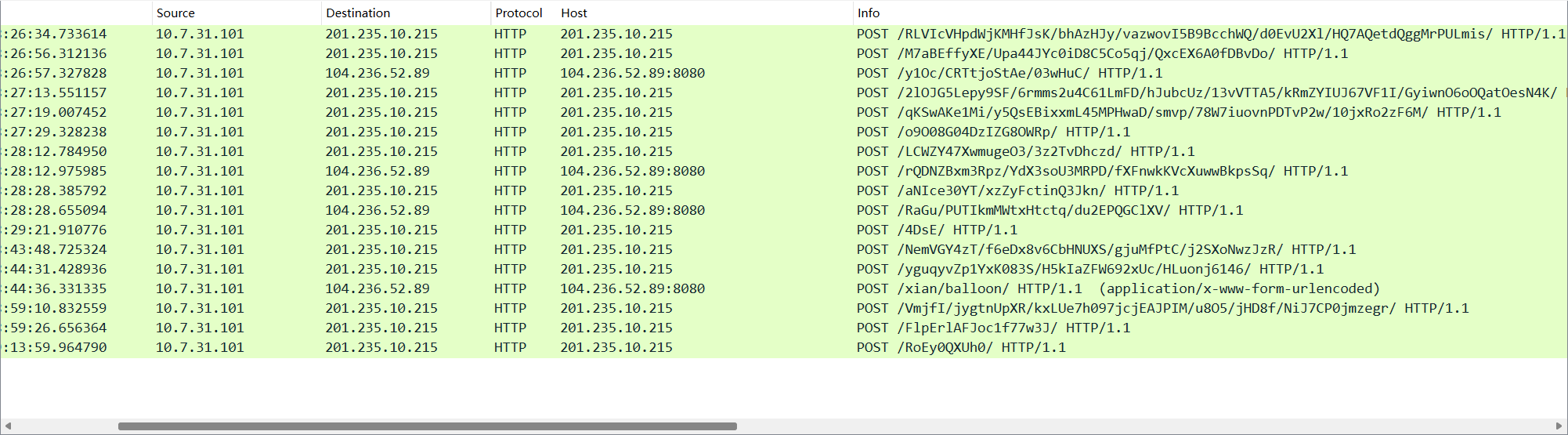
随后不断的向201.235.10.215 IP地址POST数据
将doc文件和exe文件导出(注意:请勿在个人电脑上导出,请在虚拟机内导出)
使用binwalk对doc文件进行分析
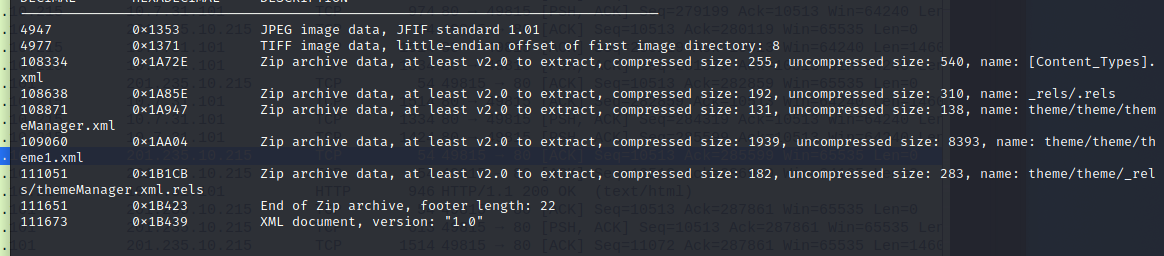
使用foremost将文件导出,发现有一个ole文件夹和一个zip文件夹,zip文件内为xml文件
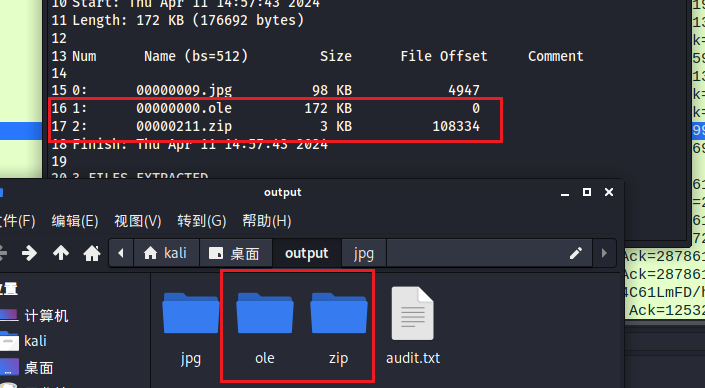
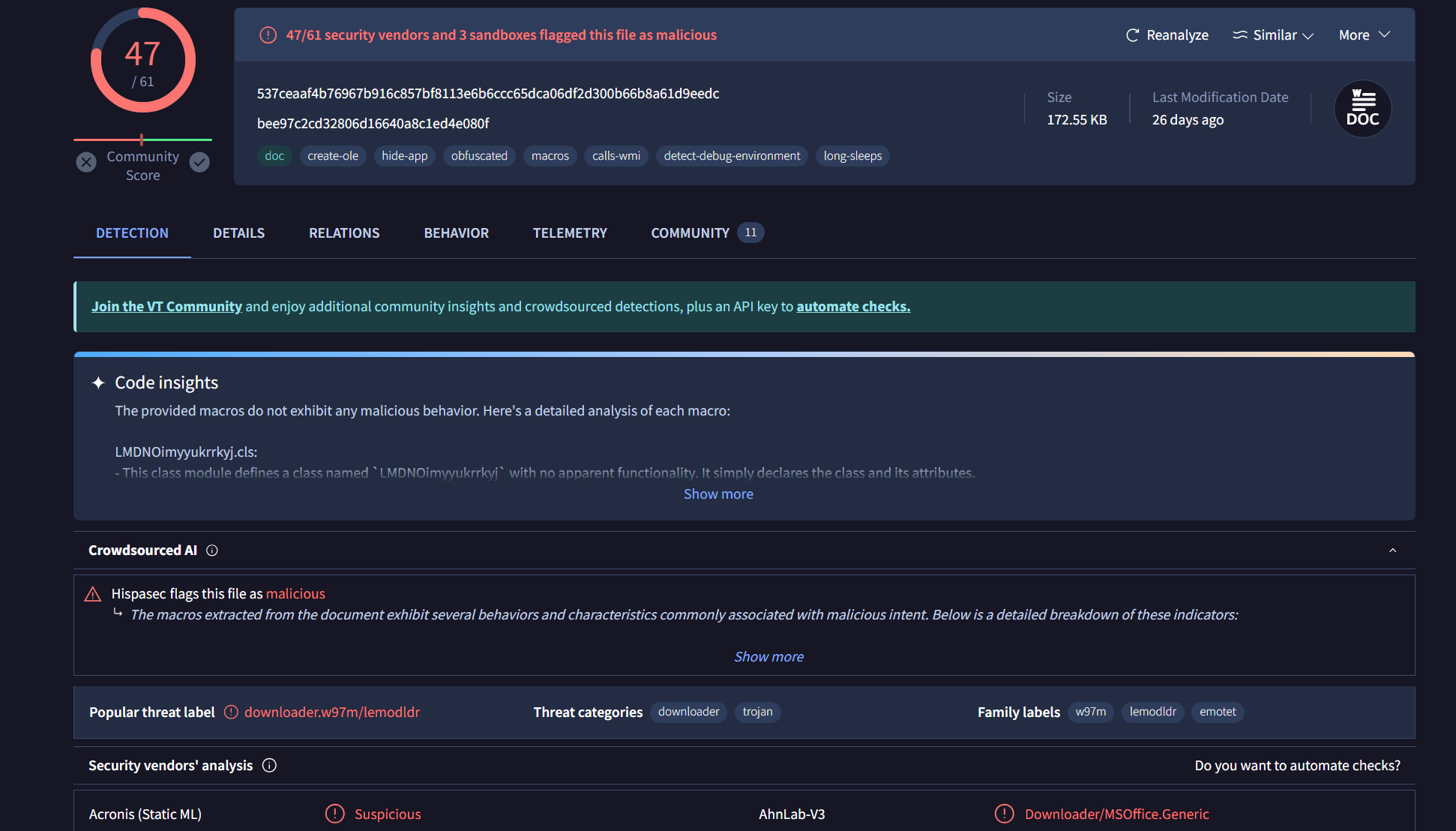
计算.ole文件的MD5值,并在virustotal内查询,发现其为木马下载器,那么后续exe文件则为可执行木马程序
计算exe文件的MD5值,并在virustotal内查询,确定其为木马程序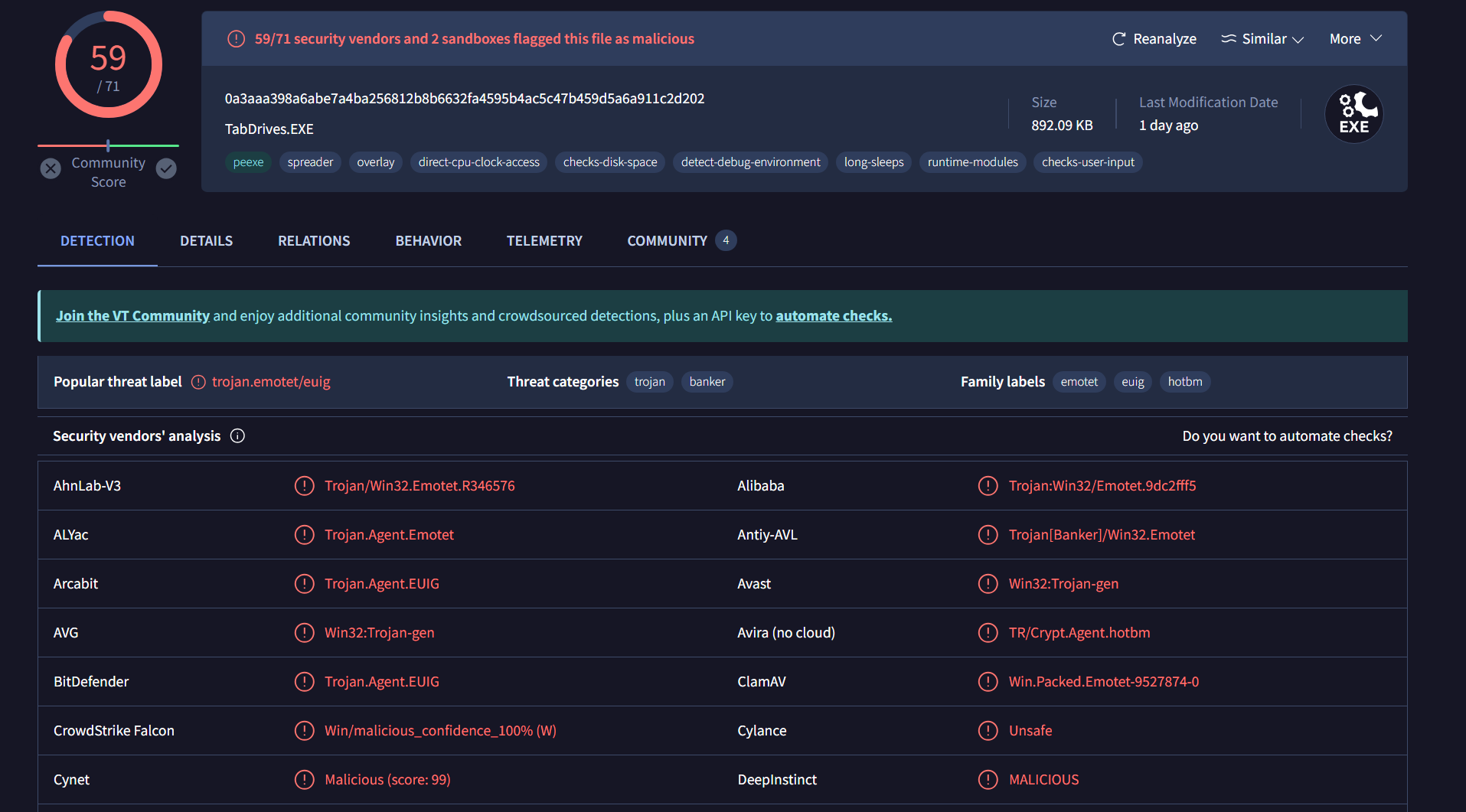
C2流量
下载木马程序之后,主机10.7.31.101与主机为201.235.10.215、104.236.52.89:8080交互频繁
加密流
无可疑地址
其他流
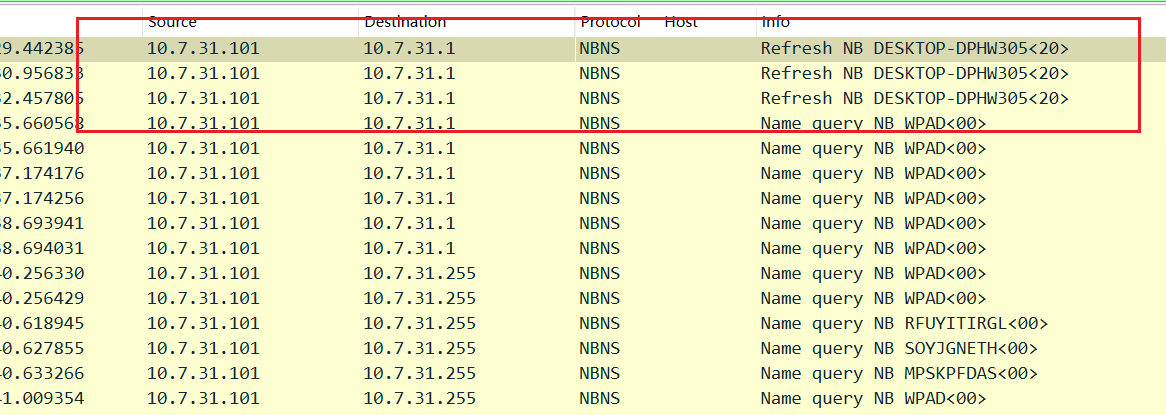
10.7.31.101发出NBNS注册请求到 NBNS 服务器,其计算机名为DESKTOP-DPHW305<20> (Server service)
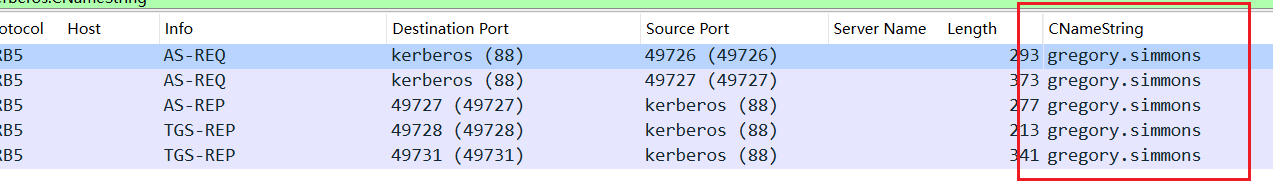
通过过滤条件kerberos.CNameString来查找账户名称
Kerberos 是一个网络身份验证协议,用于在不安全的网络中安全地验证用户和服务之间的身份。
以下是 Kerberos 协议的工作原理:
认证服务器(AS):用户向 Kerberos 认证服务器请求访问服务。AS 验证用户的身份,并生成用于与 Ticket Granting Server (TGS) 通信的 Ticket-Granting Ticket (TGT)。TGT 是受加密保护的,只有 TGS 可以解密它。
票证授予服务器(TGS):用户收到 TGT 后,可以使用它向 TGS 请求访问特定的服务。用户向 TGS 提交 TGT 和服务标识符的请求。TGS 验证用户的 TGT,并生成一个用于访问特定服务的服务票证(Service Ticket)。服务票证也是受加密保护的。
服务请求:用户收到服务票证后,可以将它与服务请求一起发送给服务。服务收到请求后,使用它和自己的密钥解密服务票证。如果票证有效且未被篡改,服务将向用户提供所需的服务。
线索梳理
- Environment(调查的资产信息/环境)
- LAN segment range:10.07.31.0/24
- Domain:tecsolutions.info
- Domain controller:10.07.31.7
- LAN segment gateway:10.07.31.1
- LAN segment broadcast address:10.07.31.255
- Incident Report
- Executive summary:
用户gregory.simmons被木马感染 - Victim details(受害者细节)
- IP address: 10.7.31.101
- MAC address: 00:0c:6e:12:af:38
- User account name: gregory.simmons
- Indicators of compromise (IOCs)
- SHA256 hash:0a3aaa398a6abe7a4ba256812b8b6632fa4595b4ac5c47b459d5a6a911c2d202
- File size:913,503 字节
- File name:3tknamb7298632293.exe
- File location:http://jambino.us/tv/DYsPb/
- File description:可执行文件
- HTTP traffic to retrieve the malware
- 191 2020-07-31 08:25:37.088661 10.7.31.101 191.6.208.51 HTTP e-dsm.com.br GET /www/ZdJCAB/ HTTP/1.1 http (80) 49737 (49737) 488 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 531 2020-07-31 08:26:19.877245 10.7.31.101 67.20.112.81 HTTP jambino.us GET /tv/DYsPb/ HTTP/1.1 http (80) 49751 (49751) 123 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- HTTP traffic for remote request infection activity
- 1493 2020-07-31 08:26:34.733614 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /RLVIcVHpdWjKMHfJsK/bhAzHJy/vazwovI5B9BcchWQ/d0EvU2Xl/HQ7AQetdQggMrPULmis/ HTTP/1.1 http (80) 49815 (49815) 414 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 1649 2020-07-31 08:26:56.312136 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /M7aBEffyXE/Upa44JYc0iD8C5Co5qj/QxcEX6A0fDBvDo/ HTTP/1.1 http (80) 49815 (49815) 414 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 1675 2020-07-31 08:26:57.327828 10.7.31.101 104.236.52.89 HTTP 104.236.52.89:8080 POST /y1Oc/CRTtjoStAe/03wHuC/ HTTP/1.1 http-alt (8080) 49817 (49817) 570 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 1842 2020-07-31 08:27:13.551157 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /2lOJG5Lepy9SF/6rmms2u4C61LmFD/hJubcUz/13vVTTA5/kRmZYIUJ67VF1I/GyiwnO6oOQatOesN4K/ HTTP/1.1 http (80) 49815 (49815) 414 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 1881 2020-07-31 08:27:19.007452 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /qKSwAKe1Mi/y5QsEBixxmL45MPHwaD/smvp/78W7iuovnPDTvP2w/10jxRo2zF6M/ HTTP/1.1 http (80) 49815 (49815) 414 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 2003 2020-07-31 08:27:29.328238 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /o9O08G04DzIZG8OWRp/ HTTP/1.1 http (80) 49815 (49815) 414 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 2543 2020-07-31 08:28:12.784950 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /LCWZY47XwmugeO3/3z2TvDhczd/ HTTP/1.1 http (80) 49815 (49815) 366 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 2558 2020-07-31 08:28:12.975985 10.7.31.101 104.236.52.89 HTTP 104.236.52.89:8080 POST /rQDNZBxm3Rpz/YdX3soU3MRPD/fXFnwkKVcXuwwBkpsSq/ HTTP/1.1 http-alt (8080) 49825 (49825) 350 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 2685 2020-07-31 08:28:28.385792 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /aNIce30YT/xzZyFctinQ3Jkn/ HTTP/1.1 http (80) 49815 (49815) 366 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 2697 2020-07-31 08:28:28.655094 10.7.31.101 104.236.52.89 HTTP 104.236.52.89:8080 POST /RaGu/PUTIkmMWtxHtctq/du2EPQGClXV/ HTTP/1.1 http-alt (8080) 49826 (49826) 1490 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 3260 2020-07-31 08:29:21.910776 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /4DsE/ HTTP/1.1 http (80) 49815 (49815) 382 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 3861 2020-07-31 08:43:48.725324 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /NemVGY4zT/f6eDx8v6CbHNUXS/gjuMfPtC/j2SXoNwzJzR/ HTTP/1.1 http (80) 49985 (49985) 366 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 4037 2020-07-31 08:44:31.428936 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /yguqyvZp1YxK083S/H5kIaZFW692xUc/HLuonj6146/ HTTP/1.1 http (80) 49985 (49985) 366 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 4064 2020-07-31 08:44:36.331335 10.7.31.101 104.236.52.89 HTTP 104.236.52.89:8080 POST /xian/balloon/ HTTP/1.1 (application/x-www-form-urlencoded) http-alt (8080) 49987 (49987) 722 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 4178 2020-07-31 08:59:10.832559 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /VmjfI/jygtnUpXR/kxLUe7h097jcjEAJPIM/u8O5/jHD8f/NiJ7CP0jmzegr/ HTTP/1.1 http (80) 49989 (49989) 366 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 4414 2020-07-31 08:59:26.656364 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /FlpErlAFJoc1f77w3J/ HTTP/1.1 http (80) 49989 (49989) 366 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- 4574 2020-07-31 09:13:59.964790 10.7.31.101 201.235.10.215 HTTP 201.235.10.215 POST /RoEy0QXUh0/ HTTP/1.1 http (80) 49999 (49999) 366 ASUSTekCOMPU_12:af:38 Cisco_79:48:c2
- INVESTIGATION
- 首先检查http传输的exe可执行文件
- 发现C2流量
- Executive summary:
知识
DCERPC
DCERPC(Distributed Computing Environment Remote Procedure Calls)是一种远程过程调用(RPC)协议,用于在分布式计算环境中进行通信。它最初是由OSF(Open Software Foundation)开发的,后来成为了 DCE(Distributed Computing Environment)标准的一部分。
DRSUAPI
DRSUAPI(Directory Replication Service Remote Administration Interface)是用于管理 Windows 活动目录(Active Directory)复制服务的远程管理接口。它提供了一组用于管理和监视活动目录复制的远程过程调用(RPC)接口。
LLMNR
LLMNR 是 Link-Local Multicast Name Resolution 的缩写,是一种用于在局域网中进行主机名解析的协议。它通常用于 Windows 系统中,并且是 Windows Vista 及更高版本中的默认网络服务之一。
LDAP
LDAP 是 Lightweight Directory Access Protocol 的缩写,是一种用于访问和维护分布式目录服务的协议。它最初是由大学提供的工具和服务的联合开发团队(University of Michigan)开发的,并成为了互联网工程任务组(IETF)的标准协议。