TRAFFIC ANALYSIS EXERCISE - FRANK-N-TED (WHAT'S GOING ON?)
2020-06-12 - TRAFFIC ANALYSIS EXERCISE - FRANK-N-TED (WHAT’S GOING ON?)
学习记录
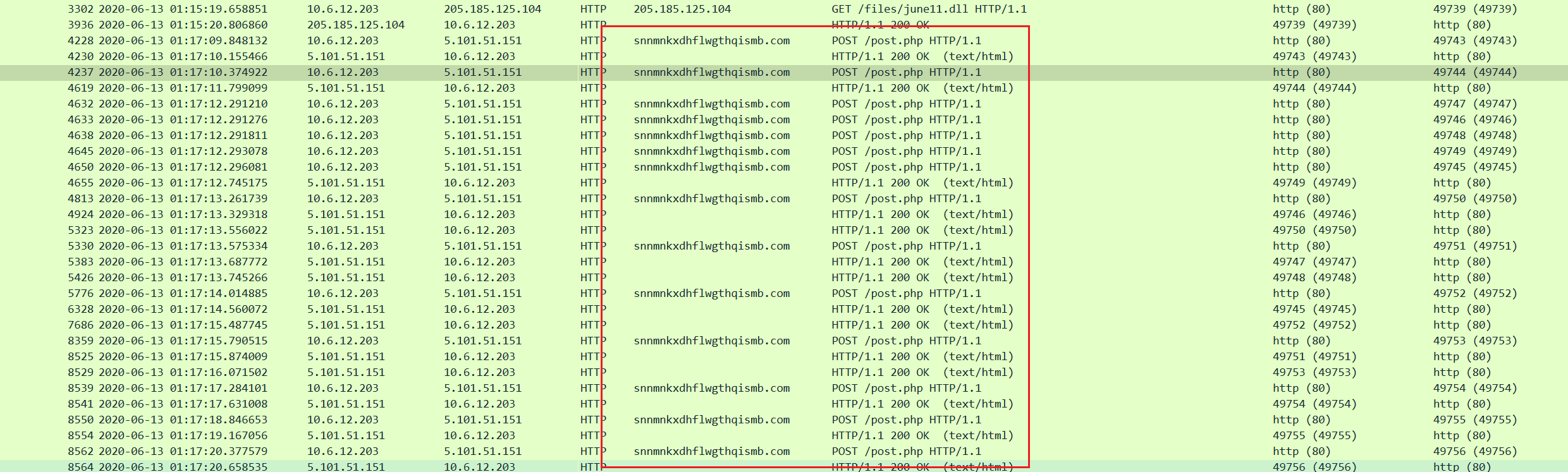
HTTP流
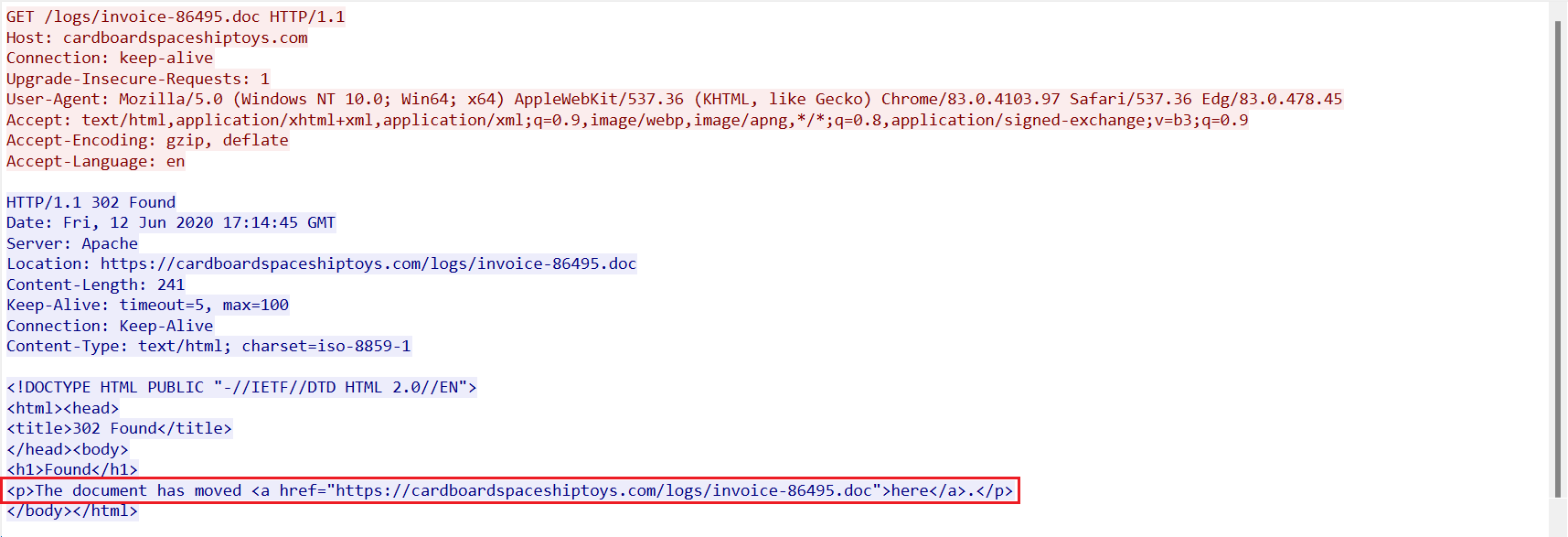
首先查看HTTP流,然后追踪第一条流
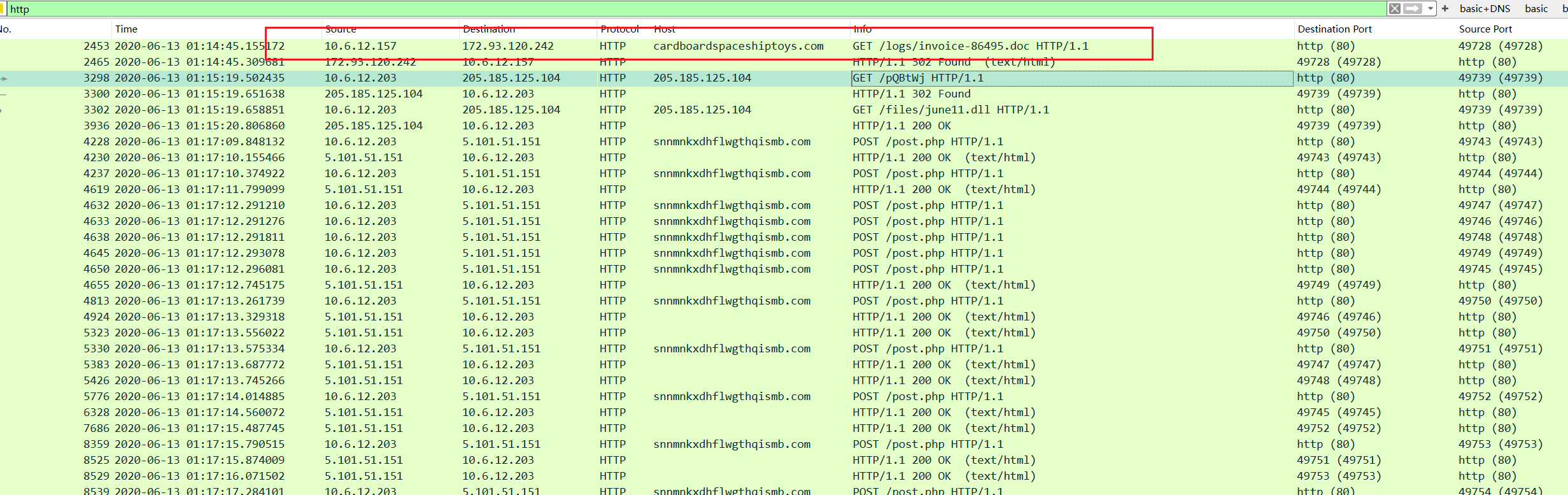
提示document被转移,猜测用户访问http://cardboardspaceshiptoys.com/logs/invoice-86495.doc后,又点击https://cardboardspaceshiptoys.com/logs/invoice-86495.doc
随后追踪后两条HTTP流
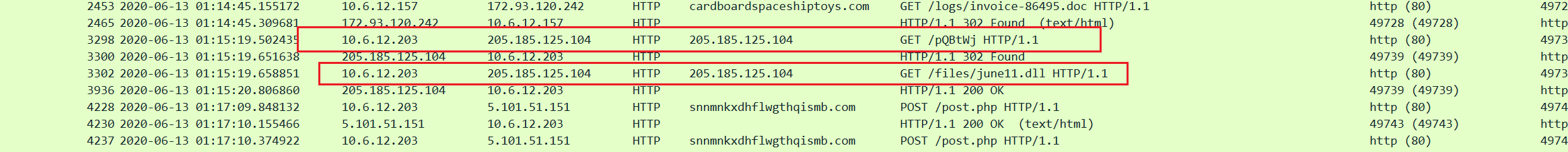
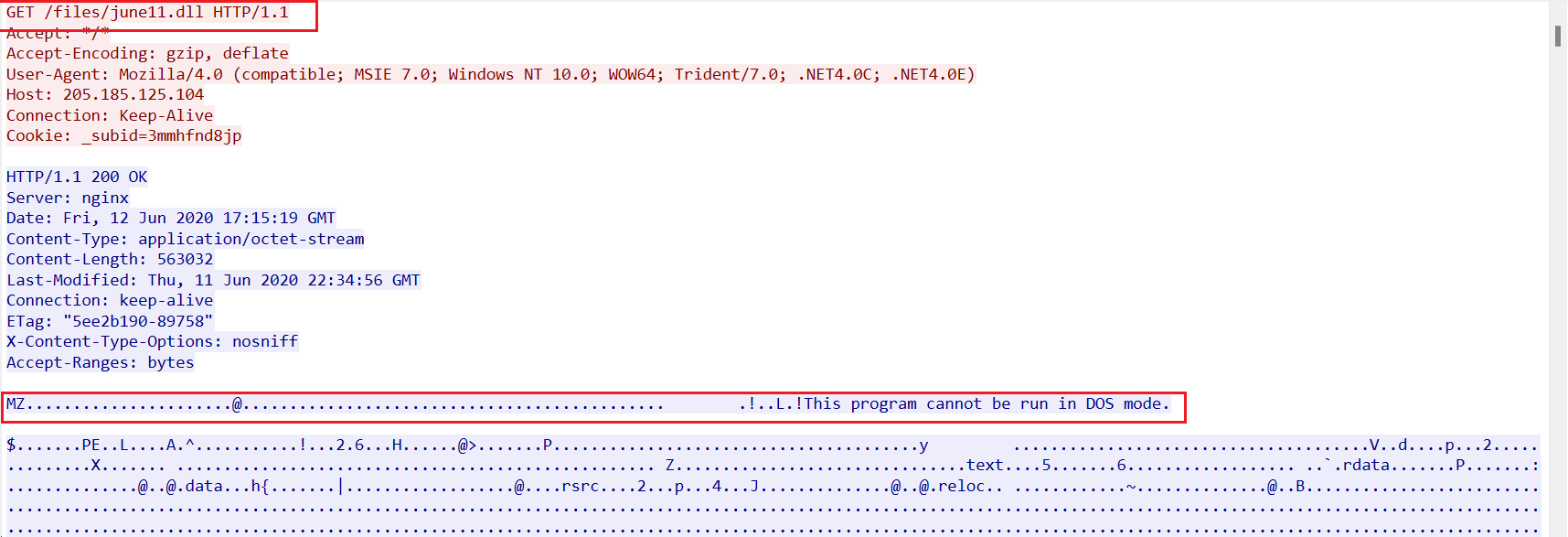
发现在GET http://205.185.125.104/files/june11.dll后,响应了一个可执行文件
随后对http://snnmnkxdhflwgthqismb.com/post.php进行了一系列POST REQUEST
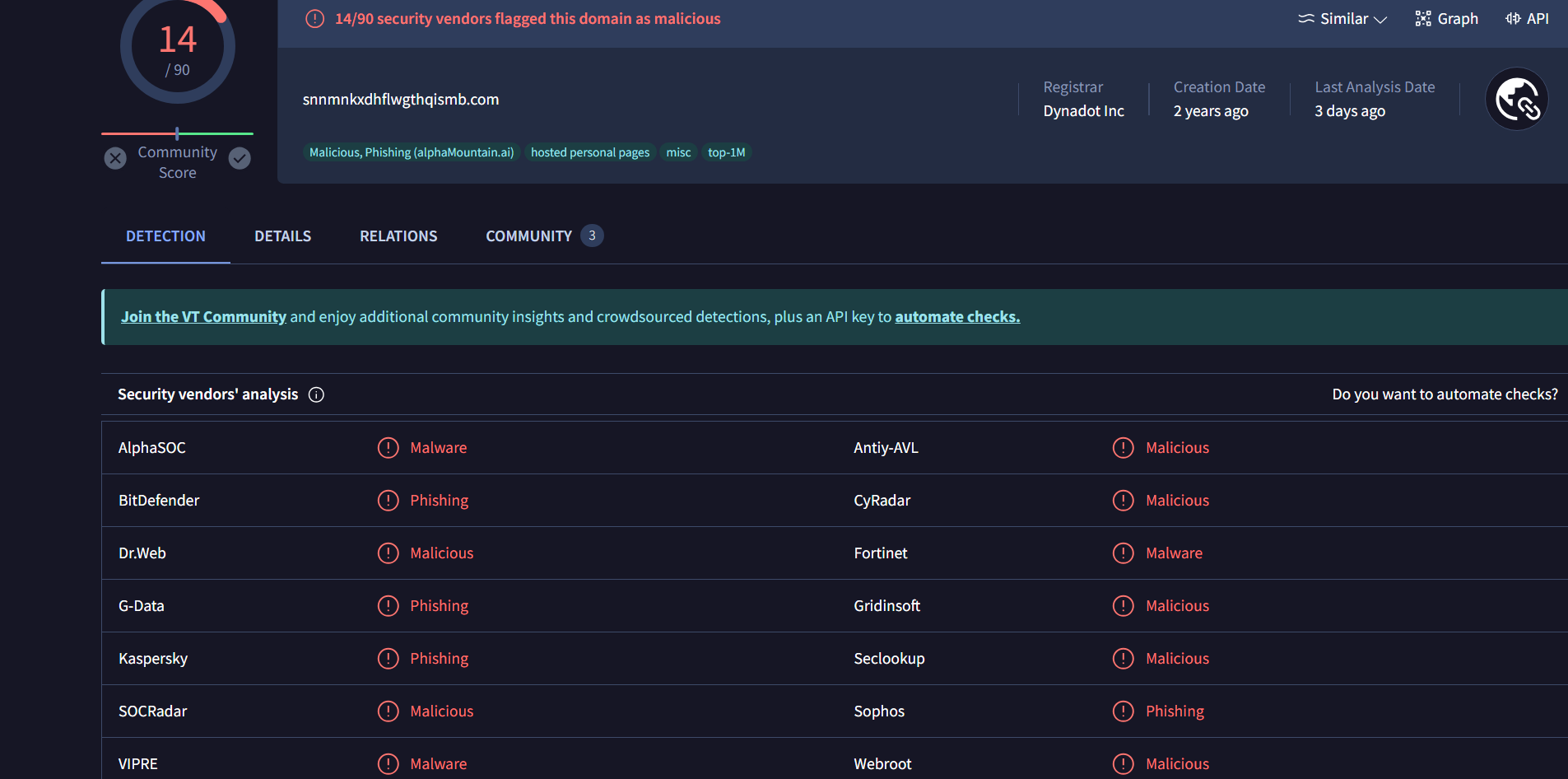
利用virustotal查询域名snnmnkxdhflwgthqismb.com
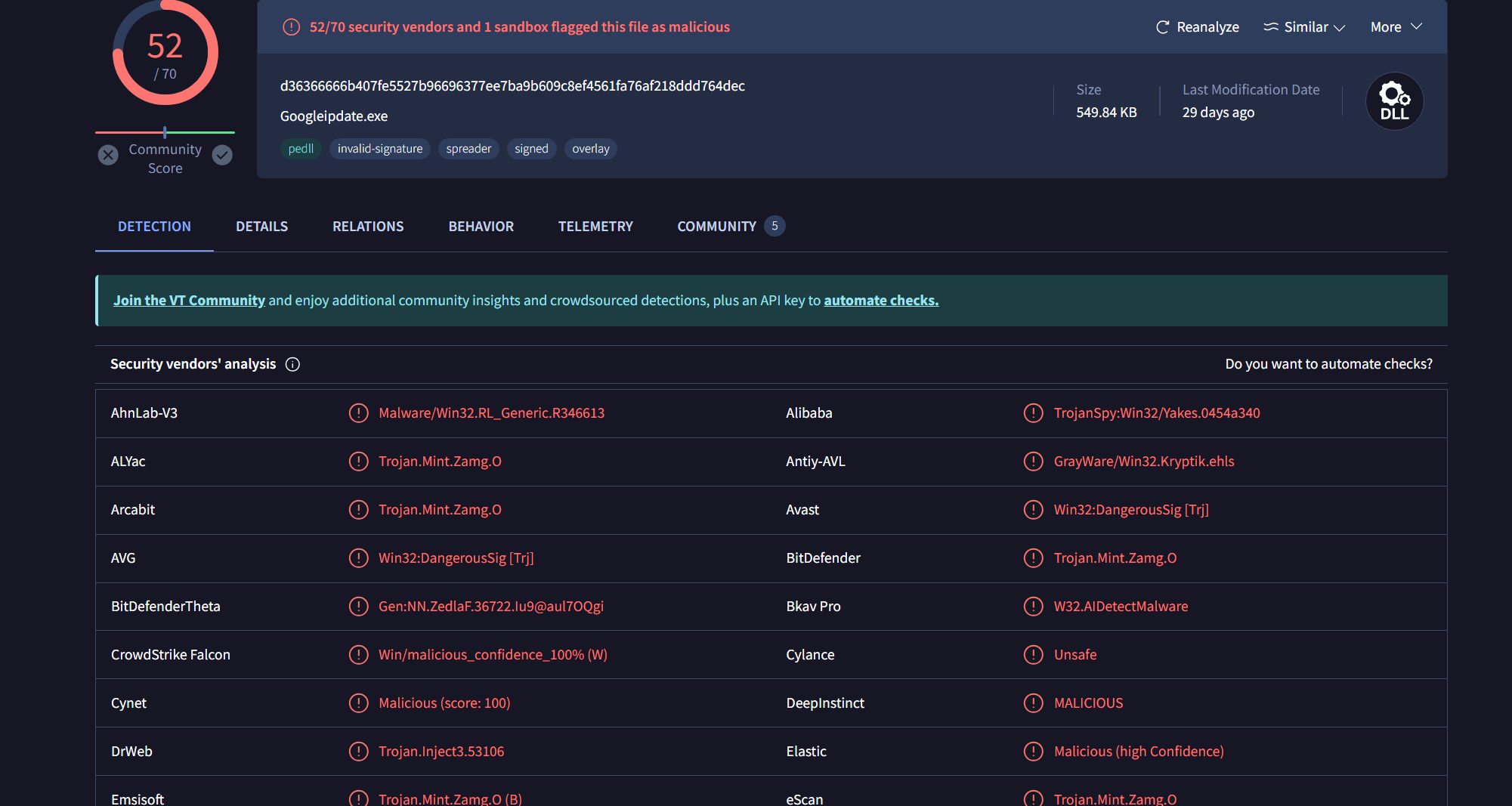
在虚拟机中导出.dll文件,并计算其sha256值,并进行查询,其为恶意软件
加密流
利用tls.handshake.type eq 1过滤条件查询握手信息,好像没什么信息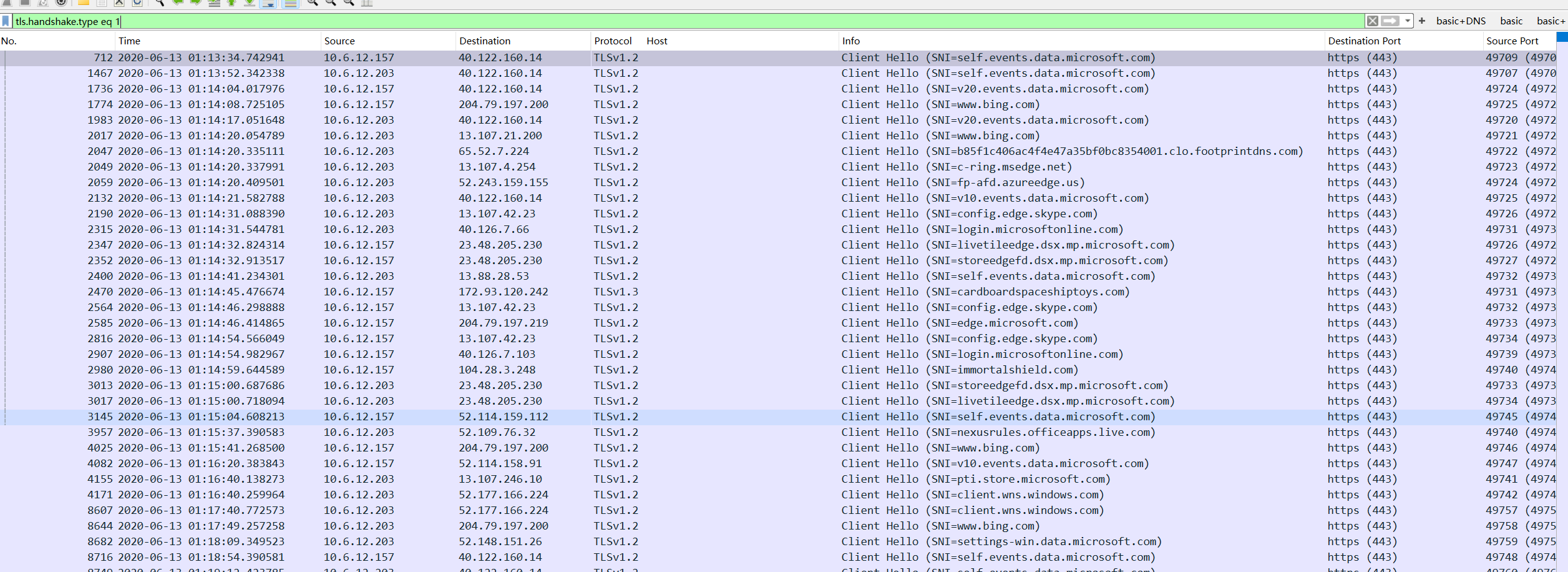
线索梳理
- Environment(调查的资产信息/环境)
- LAN segment range:10.6.12.0/24
- Domain:frank-n-ted.com
- Domain controller:frank-n-ted-dc-10.6.12.12
- LAN segment gateway:10.6.12.1
- LAN segment broadcast address:10.6.12.255
- Incident Report
Executive summary:
LAPTOP-5WKHX9YG的用户frank.brokowski访问http://205.185.125.104/files/june11.dll被感染
Victim details
- IP address:10.6.12.203
- MAC address:Intel_6d:fc:e2 (84:3a:4b:6d:fc:e2)
- User account name:frank.brokowsk
Indicators of compromise (IOCs)
- SHA256 hash:d36366666b407fe5527b96696377ee7ba9b609c8ef4561fa76af218ddd764dec
- File size:563,032 字节
- File name:june11.dll
- File location:http://205.185.125.104/files/june11.dll
- File description:恶意程序
HTTP traffic to retrieve the malware
3302 2020-06-13 01:15:19.658851 10.6.12.203 205.185.125.104 HTTP 205.185.125.104 GET /files/june11.dll HTTP/1.1 http (80) 49739 (49739) 312 Intel_6d:fc:e2 Cisco_29:41:7d
HTTP traffic for remote request infection activity
4228 2020-06-13 01:17:09.848132 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49743 (49743) 713 Intel_6d:fc:e2 Cisco_29:41:7d
4237 2020-06-13 01:17:10.374922 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49744 (49744) 749 Intel_6d:fc:e2 Cisco_29:41:7d
4632 2020-06-13 01:17:12.291210 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49747 (49747) 646 Intel_6d:fc:e2 Cisco_29:41:7d
4633 2020-06-13 01:17:12.291276 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49746 (49746) 584 Intel_6d:fc:e2 Cisco_29:41:7d
4638 2020-06-13 01:17:12.291811 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49748 (49748) 579 Intel_6d:fc:e2 Cisco_29:41:7d
4645 2020-06-13 01:17:12.293078 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49749 (49749) 705 Intel_6d:fc:e2 Cisco_29:41:7d
4650 2020-06-13 01:17:12.296081 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49745 (49745) 649 Intel_6d:fc:e2 Cisco_29:41:7d
4813 2020-06-13 01:17:13.261739 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49750 (49750) 638 Intel_6d:fc:e2 Cisco_29:41:7d
5330 2020-06-13 01:17:13.575334 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49751 (49751) 585 Intel_6d:fc:e2 Cisco_29:41:7d
5776 2020-06-13 01:17:14.014885 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49752 (49752) 668 Intel_6d:fc:e2 Cisco_29:41:7d
8359 2020-06-13 01:17:15.790515 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49753 (49753) 816 Intel_6d:fc:e2 Cisco_29:41:7d
8539 2020-06-13 01:17:17.284101 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49754 (49754) 890 Intel_6d:fc:e2 Cisco_29:41:7d
8550 2020-06-13 01:17:18.846653 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49755 (49755) 798 Intel_6d:fc:e2 Cisco_29:41:7d
8562 2020-06-13 01:17:20.377579 10.6.12.203 5.101.51.151 HTTP snnmnkxdhflwgthqismb.com POST /post.php HTTP/1.1 http (80) 49756 (49756) 918 Intel_6d:fc:e2 Cisco_29:41:7d